Introduction
In the world of Cybersecurity today, one of the biggest
issues that has come about is to what degree do you trust an individual when it
comes to accessing your digital assets that reside in your IT
Infrastructure. It all comes down to
confirming without a shadow of a doubt the identity of the individual that is
going to access your shared network resources.
The concept of a so called Zero Trust Model has started to
make ripples, but the main flaw with this is that you are presumably trusting nobody
at first.
While this may sound great in theory, when it comes to
applying this to real world situations, it is an almost impossible task to
do. The problem is that even with this
kind of approach, there could always be some issue of trust, no matter through
how many layers of authentication that certain individual has gone through.
Therefore, there has to be some degree of implicit trust
with the people who will gain access to inside your digital assets. This is where the Circle of Trust Model comes
into play and is the focal point of this article.
The Concept of
the Circle of Trust
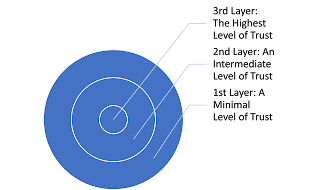
This model creates certain barriers, as to where the circles
will be drawn depending upon where the level of trust will be placed at, when
it comes to determining what kinds of data will be shared. Imagine these
circles being implemented inside your IT Infrastructure as follows:
As can be seen from the above illustration, the First Layer involves just a baseline of trust. In this situation, the individual must be fully authenticated with all of the mechanisms that are available. In this instance, there is no access that can be given to any shared network resources, even if the data is deemed to be non-proprietary in nature. In the Second Layer, there is now a 50% percent trust that has been established, because he or she has been more or less fully vetted by getting through the First Layer. In this scenario, the person can then gain access to those shared resources that contain an equal combination of both non-proprietary as well as propriety data.
Finally, in the Third Layer,
after being further scrutinized by more defense mechanisms, the individual will
now have access to 100% (if not most) to all of the proprietary data that the
company has in their databases. At this
juncture, there has been the highest level of trust placed upon them.
It is important to keep in
mind that the above illustration is just a very simplistic view of the concept
of the Circles of Trust. There will of
course be many more circles that can be incorporated, but this all depends upon
what your security requirements are, and if you also want to impose even more
varying Layers of Trust.
In other words, it won’t be
as cut and dry as a three step process.
For example, you will obviously
first start with a baseline of trust.
Then that may increase in only incremental levels until the individual
has reached the plateau of an intermediate level of trust. Then, you may even deploy further degrees of
trust, because after all, once they have the reached third level, you are
almost trusting he or she without any question at all.
The Circles of Trust model
also undescores one fundamental and extremely rule in Cybersecurity: It is very important to have more than one
line of defense, as it is exemplified by the three circles up above. For example, although the word “trust” has
been associated with them, they also imply that a business is going to install
at three layers of defense, and probaly even more.
So, another way to view the
Circles of Trust is to consider them as a muti tiered security model. For example, if a Cyberattacker were to break
through the first circle, then the statistical probability that they will break
through the second and even the third circles becomes substantially lower.
Still, ther is always that
chance a Cyberattacker can still break through all layers of defenses. The only thing that can be done is mitigating
that risk as much as possible. Deploying this kind of approach, takes a
multitude of security technologies, which are further described in the next
section.
What Are the Security Tools That Are Needed?
When it comes to implementing
this kind multi tiered approach, there are numerous tools out there that a
business can deploy, but some of the more common ones are as follows:
1)
The Firewall:
This
kind of technology has advanced to the point where there are now differing
kinds of them, which include:
Ø Proxy Firewalls;
Ø Stateful Inspection Firewalls;
Ø Unfied Threat Management (UTM) Firewalls;
Ø Next Generation Firewalls (NGWs).
On a
fundamental level, the Firewall carefully examines all data packets that are
both inbound and outbound to/from the IT Infrastructure. Its primary goal is to track down and
intercept those data packets that are deemed to be malicious in nature, and to
prevent them from entering into the Circles of Trust, at the very first
layer. This is typically done by using a
set of presetablished rules which have been set forth by the network
administrator. Firewalls have been been
a trusted means of defense for a quite a long time, going back as far as 25
years. The most common notion of a
Firewall is that they are simply hardware devices, but they can also be
software based as well.
2)
Routers:
A
router serves the same function as a firewall, but also, it adds one more
component: It’s other primary role is to
forward the data packets in the most optimal and efficient manner possible so
that it reaches its final destination in the shortest time possible, without
causing any kinds of network congestion.
In other words, in the real world, a data packet simply just not arrives
at its final destination in just one fell swoop. Depending upon how the network topology is
laid out, data packets typically go from one to another. The specific route that these data packets
are primarily dependent upon the Access Control Lists that have been set forth
by the network administator.
3)
Intrusion
Detection Systems:
This
kind of security tool are often referred to as “IDSs”, and there are two main
types of them:
Ø The Network Intrusion Devices (aka “NIDs”);
Ø The Host based Intrusion Detection System (aka
“HIDs”).
The
first is used to analyze the flow of network traffic to and from the IT
Infrastructure, and the second is typicallu used inspect the critical files of
a server based operating system. But
which ever one is used, the primary advantage of using them is that they can be
easily connected to a SIEM, which stands for a “Security Information and Event
Management” system. This can be used to
alert the IT Security team of any abnormal or analamous network traffic
patterns that take place. The SIEM can
also be used to filter for false positives and only present the legitimate
threat warnings and alerts.
4)
Virtual
Private Networks (VPNs):
This
is what is used most typically when connecting from a remote location to the IT
Infrastructure. With this, a private (as
well as secure) network communications flow is established using the public
Internet. The VPN will literally mask
your IP Address, so that it cannot be easily intercepted by a malicious third
party. Also, as a further layer of
protection, the data packet payload is encapsulated, wrapped into, another data
packet.
5)
Endpoint
Security:
This
is a crucial area in the Circles of Trust that needs to be fortified. Many businesses have ignored this, and have
typically focused upon securing only the network lines of communications. With this both the point of origination
(which is the device of the end user) and the point of destination (which is
the corporate server) are further by using either a firewall, router, or an
intrusion detection device, or perhaps even a combnation of all three. These can all be either hardware or software
based.
Conclusions
Overall, this article has
examined in closer detail the model of the Circles of Trust, and the security
technologies that can be used in it. Where
to put them exactly in the Circles of Trust is once again largely dependent
upon your security requirements.
But, there is one thing to
keep in mind: Simply dpeloying these
tools in large numbers is not the answer.
This can become quite costly, and even increase the attack surface for
the Cyberattacker.
Therefore, it is very
important to conduct a Risk Analysis first, in order to determine where they
should be strategically placed instead.
Sources
1)
https://www.cisco.com/c/en/us/products/security/firewalls/what-is-a-firewall.html